Introduction
APIs are no longer just technical connectors; they are the nervous system of modern digital business. As enterprises are adopting an API-First approach to fuel their AI journey, APIs have evolved from being used as integrators to monetized assets. As a result, they have become more vulnerable than ever due to the massive expansion of the attack surface and the shift from simple internal integrations to complex, public-facing revenue streams that bypass traditional perimeter defenses. APIs are now a business and reputational risk as they have become the number one attack vector for cybercriminals seeking to steal sensitive data or disrupt services.
The terrifying reality of modern cybersecurity is that a perfectly valid HTTP request can still be an attack. If a user successfully authenticates and requests data they are technically allowed to see, but they do it 100,000 times an hour to scrape your entire database, that’s a breach.
Traditional security measures are increasingly failing to spot these "business logic" attacks. To protect the API economy, we need smarter, deeper defenses. This is where Google Cloud’s Apigee Advanced API Security enters the picture. Helping to protect against behavioral, contextual, and intelligent attacks threatened by today’s AI-generated security threats.
Understanding Apigee’s Advanced API Security
Apigee’s Advanced API Security (AAS) provides enterprise-grade security capabilities for the Apigee API management platform. It leverages Google's proprietary machine learning models to identify sophisticated API abuse patterns and security threats that conventional security tools often miss.
Standard API Security includes mechanisms like OAuth2 for authorization, mTLS for authentication, basic rate limiting to prevent accidental floods, and checking for well-known vulnerabilities like SQL injection or cross-site scripting (XSS) in payloads. However, AAS introduces adaptive, behavior-aware defenses that is designed to detect attacks that look legitimate on the surface but are malicious in intent.
AAS is a set of capabilities built specifically to identify “abuse” rather than just “hacking”. It uses AI and ML to analyze traffic patterns over time, establishing a baseline of normal behavior for your specific APIs. Once it knows what “normal” looks like, it can spot deviations that indicate automated threats, such as:
- Advanced API Scraper: A machine learning model that detects API scraping, which is the process of extracting targeted information from APIs for malicious purposes.
- Advanced Anomaly Detection: A machine learning model for detecting anomalies - unusual patterns of events - in API traffic.
- Brute Guessor: High proportion of response errors (4xx and 5xx) during the previous 24 hours
- Flooder: High proportion of traffic from an IP address in a 5-minute window
- OAuth Abuser: Large number of OAuth sessions with a small number of user agents during the previous 24 hours
- Robot Abuser: A large number of 403 rejection errors in the past 24 hours
- Static Content Scraper: High proportion of response payload size from an IP address in a 5-minute window
- TorListRule: Tor (The Onion Router) is a network used to anonymize internet traffic by routing it through a series of volunteer-operated servers (nodes). A Tor exit node is the last Tor node that traffic passes through in the Tor network before exiting to the Internet. Detecting Tor exit nodes indicates that an agent has sent traffic to your APIs from the Tor network, possibly for malicious purposes.
3 Architectural Positioning and Differentiation from Web Application Firewall (WAF)
3.1 The WAF: The Outer Perimeter Bouncer
Imagine your application architecture as a secure building. Web Application Firewall (WAF) is the bouncer at the very front gate.
It operates primarily at the network edge (Layers 3, 4, and generic Layer 7). It is incredibly efficient at blocking high-volume, noisy attacks before they ever reach your infrastructure.
3.2 AAS: The Interior API Security Specialist
AAS sits much deeper inside the building, specifically within the API Gateway layer, after the TLS termination and after the initial WAF inspection.
Because AAS sits right next to the API logic, it understands the context of the traffic in a way a WAF never can. A WAF sees an HTTP POST request; Apigee sees a "Login attempt for User X followed immediately by a Password Reset request for User Y".
A WAF might see a request from a clean IP address and let it through. Apigee AAS, however, might recognize that although the IP is clean, the token being used has shown suspicious behavior across 50 other IPs in the last ten minutes.
3.3 Architectural Positioning
The WAF acts as the first line of defense for API traffic, protecting the external load balancer and mitigating large-scale threats such as DDoS attacks and common web-based vulnerabilities. Advanced API Security complements this protection by adding a deeper layer of API-specific intelligence and governance. It ensures that traffic permitted by WAF complies with defined API security policies and is safeguarded against sophisticated abuse patterns at the API gateway level.
Together, these services deliver a robust, multi-layered security architecture.
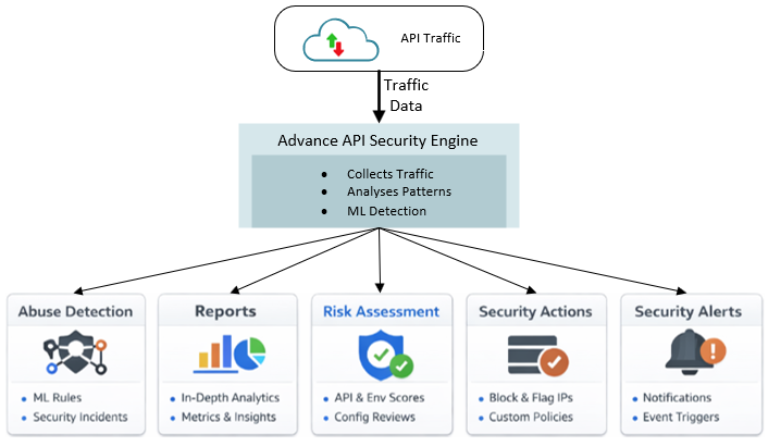
4 How Advanced API Security Works?

- As API traffic flows through Apigee, AAS collects rich metadata without inspecting sensitive payload data (PII). It looks at headers, IP addresses, access tokens, user agents, API paths being accessed, time of day, and geo-velocity (how quickly a user appears to move geographically).
- The system uses unsupervised machine learning models to build profiles of your APIs.
- Once the baseline is established, the system detects deviations. It uses specialized models for different threat types.
4.1 AAS features
5 Best Practices for Maximum Effectiveness
- Enable ML Model Training:
Opt in to machine-learning training so AAS can learn your normal traffic patterns. This enables accurate anomaly detection, with data used only within your organization. Apigee recommends that you have at least 2 weeks of historical API traffic data, and for more accurate results, 12 weeks of historical data is preferable.
- Mitigate Large Numbers of False Positives:
Correctly capture real client IPs by preserving X-Forwarded-For (XFF) headers when using proxies or load balancers. This prevents false anomalies caused by aggregated traffic from intermediary IPs.
- Exclude Trusted Traffic from Abuse Detection:
Exclude known, trusted traffic (such as automated testing or probing IPs) from abuse detection to avoid false positives. Use exclusion lists with CIDR ranges or specific IP addresses and document the reasons for each exclusion.
- Adopt a Layered Security Architecture:
Use AAS as part of a broader security strategy. Deploy WAF for edge protection and Advanced API Security for deep, API-level threat detection.
- Integrate with Zero Trust Architecture:
Position AAS as a Policy Enforcement Point in a Zero Trust model. Enable continuous, behavior-based trust evaluation with dynamic, risk-driven access decisions.
- Perform Regular Security Posture Reviews:
Use Risk Assessment features to review API configurations frequently. Act on security scores and recommendations to strengthen protections and reduce exposure.
- Configure Targeted Security Alerts:
Set up alerts for high-risk incidents and unusual traffic patterns instead of relying solely on dashboards. This reduces alert fatigue while maintaining critical visibility.
6 Business Outcomes and Use Cases of Advanced API Security
The following are a few of the use cases to consider when integrating Advanced API Security (AAS) into your architecture. Each use case demonstrates how AAS helps address specific security challenges while enabling the corresponding business outcomes outlined below.
6.1 Use Case 1: Shadow API Discovery
- Description:
To accelerate delivery, developers may deploy APIs without registering them in the API gateway. These unregistered, or “shadow,” APIs often access sensitive data but lack proper authentication and security controls, making them attractive targets for attackers.
- Solution:
AAS integrates with Load Balancers to analyze traffic patterns and identify API traffic that exists outside of managed API proxies.
- Business Outcome:
AAS automatically discovers undocumented (“shadow”) APIs across your organizations, eliminating security blind spots that are frequently exploited due to missing or inconsistent security controls.
6.2 Use Case 2: “Low and Slow” Data Scraping Attacks
- Description:
A competitor leverages a botnet to systematically scrape your product catalog and pricing data at regular intervals. By frequently rotating IP addresses, the attacker evades traditional WAF-based detection.
- Solution:
Advanced API Security correlates traffic using multiple signals such as API keys, user behavior, and access patterns—not just IP addresses. It detects abnormal activity, such as a single user accessing resources at unrealistically high speeds, even when requests originate from different IPs.
- Business Outcome:
Traditional WAFs struggle to detect business logic attacks, such as authorized users scraping sensitive data or enumerating order IDs. AAS uses machine learning to differentiate legitimate users from abusive automation, protecting revenue, sensitive data, and overall business integrity.
6.3 Use Case 3: Security Configuration Drift
- Description:
In the rush to deploy a hotfix, a developer may unintentionally disable critical security policies, such as Spike Arrest or Content Validation, on a production API proxy.
- Solution:
Advanced API Security continuously scans API proxy configurations and assigns a comprehensive security score to the environment.
- Business Outcome:
Rather than relying on periodic manual audits, AAS continuously evaluates API configurations against security best practices. It proactively flags proxies with missing authentication, weak encryption, or misconfigured policies, ensuring continuous compliance and 24/7 audit readiness.
7 Conclusion
As digital ecosystems grow increasingly complex, relying solely on traditional security measures like WAFs and basic authentication is no longer sufficient. API and Security Architects must shift their focus toward augmenting existing investments with intelligent, adaptive defenses capable of countering sophisticated threats. It is critical to plan for a security posture that goes beyond static vulnerabilities, building robust protection against behavioral, contextual, and intelligent attacks. AI-enabled solutions are essential in this new landscape, providing the continuous learning required to spot anomalies that human analysts might miss. Apigee Advanced API Security is uniquely suited to this challenge, offering the deep visibility and machine learning capabilities necessary to secure the very heart of the modern digital business.
Tag(s):
API Management
,
Artificial Intelligence
,
Apigee
,
Apigee Hybrid
,
API Gateway
,
Apigee X
,
AI Toolkit
,
AI
Siddhesh Naik - Manager, API Management and Integration
Siddhesh Naik, Manager at Blue Altair, excels in delivering enterprise-scale API management and cloud solutions. With over a decade of experience, he architects secure platforms, leads transformations and builds capabilities. He holds a Bachelor's in Computer Engineering from the University of Mumbai.